Safeguarding Financial Data in Today’s Digital Landscape
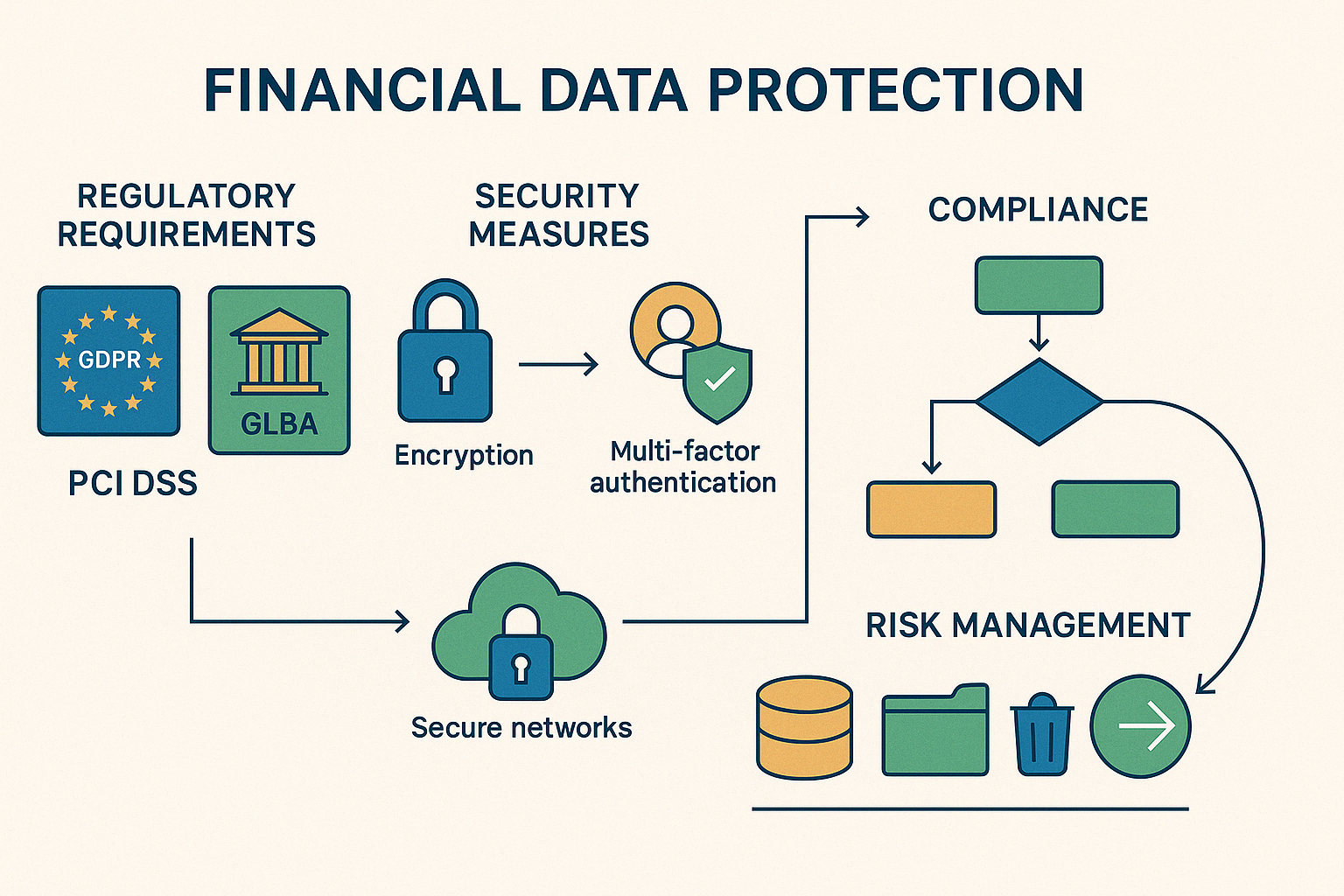
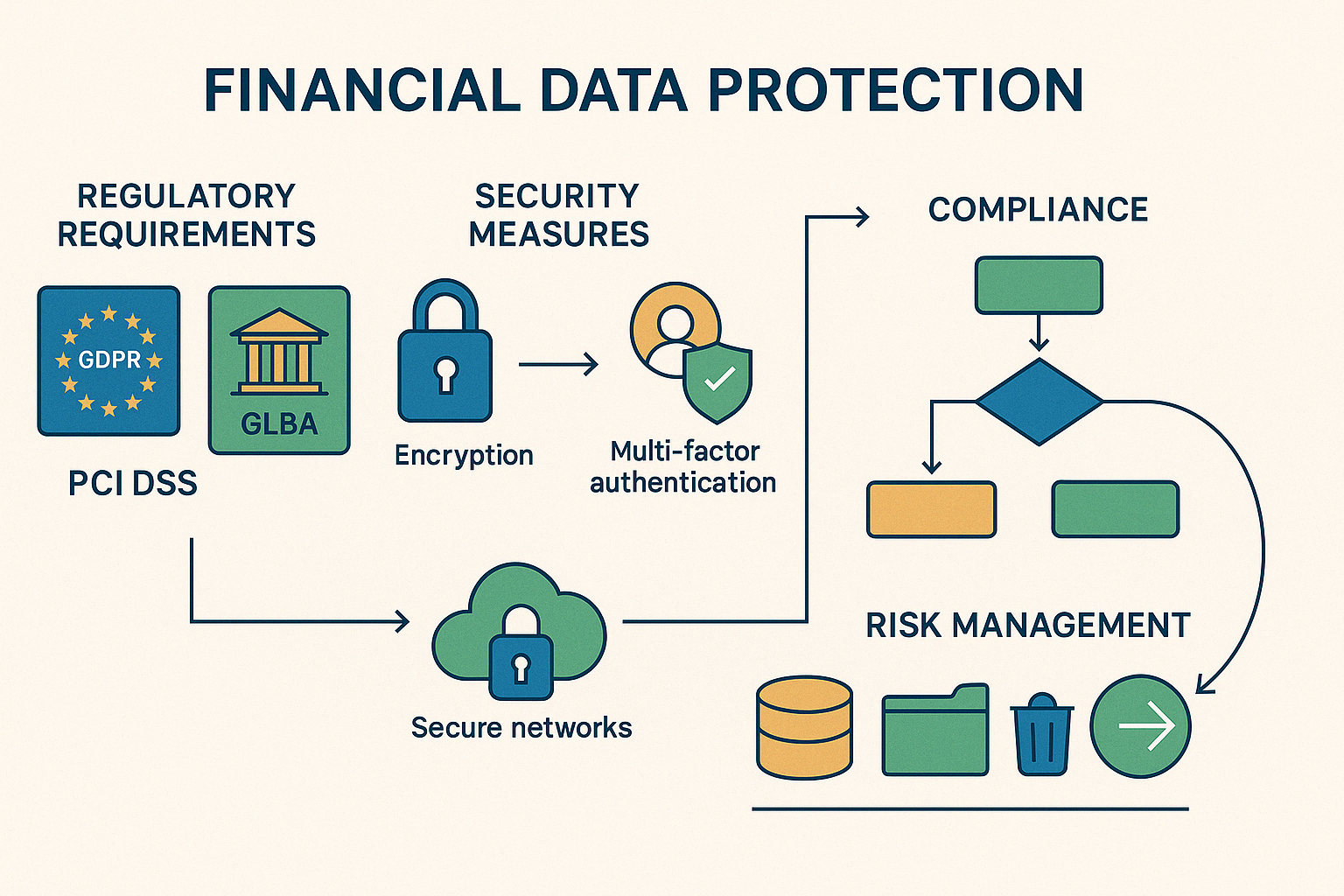
Data protection for financial services is essential for safeguarding sensitive customer information, maintaining regulatory compliance, and preserving trust in an increasingly digital financial ecosystem.
Here’s a quick overview of what financial data protection entails:
- Security Measures: Encryption, multi-factor authentication, and secure networks
- Regulatory Compliance: Adherence to GDPR, GLBA, PCI DSS, and other regulations
- Risk Management: Regular assessments, employee training, and incident response plans
- Data Governance: Proper data handling, storage, and retention policies
Financial institutions face unique challenges when protecting data. As the second-most targeted industry for cyber attacks, banks and financial services companies must implement robust security measures to prevent unauthorized access while maintaining operational efficiency.
“Too many Americans are stuck in financial products with lousy rates and service,” notes a CFPB Director, highlighting why proper data protection isn’t just about security—it’s about maintaining customer trust and enabling fair competition in financial services.
The stakes are incredibly high. A data breach can lead to severe consequences:
- Financial losses and remediation costs
- Regulatory penalties (up to 4% of annual revenue under GDPR)
- Damaged customer relationships and reputation
- Operational disruptions and recovery expenses
For small and medium-sized financial businesses in particular, implementing proper data protection isn’t just good practice—it’s essential for survival in today’s threat landscape.
Related content about data protection for financial services:
– data protection officer services
– data protection governance risk management and compliance
– data protection security controls
Understanding Data Protection in Financial Services
Financial data is the lifeblood of the banking industry. When we talk about data protection for financial services, we’re not just discussing a technical requirement—we’re talking about safeguarding people’s financial lives and futures.
Think about all the sensitive information that flows through financial institutions every day: your personal details like name and address, Social Security numbers, account information, credit card data, passwords, and much more. Every time you swipe your card or check your balance online, you’re trusting that your bank is protecting this information.
For financial institutions, protecting this data isn’t optional—it’s absolutely essential to their business and legally required. As one client told us recently, “We’re not just protecting data; we’re protecting our customers’ trust.”
The core principles that guide data protection for financial services are straightforward but powerful:
Confidentiality ensures that your financial information stays private and is only seen by authorized people. Integrity means your data remains accurate and complete—no one can tamper with your account balance! Availability balances security with accessibility, so you can access your information when needed. Privacy respects your rights regarding how your data is used and shared. And accountability means financial institutions take responsibility for proper data handling.
“Excellent data governance means you can trust your data today and in the future,” as one of our data governance experts puts it. This trust forms the foundation of every customer relationship in financial services.
Key Regulations in Data Protection for Financial Services
If you’ve ever wondered why banks ask so many security questions or require so many verification steps, it’s largely because financial institutions operate in one of the most heavily regulated environments when it comes to data protection.
The Gramm-Leach-Bliley Act (GLBA) stands as a cornerstone of financial data protection in the United States. It requires financial institutions to explain their information-sharing practices to customers, implement comprehensive security programs, and prohibits obtaining personal information through false pretenses. Breaking these rules can cost institutions up to $100,000 per violation, with officers potentially facing additional $10,000 fines. You can learn more about GLBA compliance at this resource.
For institutions with European customers, the General Data Protection Regulation (GDPR) adds another layer of requirements. Financial organizations must obtain explicit consent before processing data, implement data minimization practices, ensure customers can access and correct their information, report breaches quickly, and conduct regular impact assessments. The penalties here are even steeper—up to 4% of annual global revenue or €20 million, whichever is greater.
If your business handles credit cards (and which financial institution doesn’t?), the Payment Card Industry Data Security Standard (PCI DSS) applies to you. This standard requires secure networks, data encryption, strong access controls, regular security testing, robust password policies, and frequent password resets.
Other important regulations include the California Consumer Privacy Act, the New York Department of Financial Services Cybersecurity Regulation, and the Sarbanes-Oxley Act. As one of our banking clients recently told us, “Regulatory compliance used to be one aspect of our business. Now it’s become the framework everything else fits into.”
The Importance of Data Residency in Financial Services
Where your data physically lives matters more than you might think. Data residency—the physical location where information is stored and processed—has emerged as a critical issue for financial institutions.
Why does this matter? First, many countries require certain financial data to remain within their borders for legal compliance. Second, data sovereignty means different governments have varying levels of access to data stored in their territory, which can affect confidentiality. Third, proper data location ensures operational continuity during disruptions. And finally, customers often prefer their sensitive financial information to be stored in places with strong privacy protections, which builds customer trust.
For financial institutions operating globally, moving data across borders presents unique challenges. These transfers must comply with mechanisms like Standard Contractual Clauses, Binding Corporate Rules, and adequacy decisions that recognize countries with equivalent data protection standards.
This is particularly relevant for our clients in Princeton, Trenton, and Newark who serve customers with international connections. As one CISO we work with explained, “Data residency isn’t just checking a regulatory box—it’s a tangible way we demonstrate to customers that we take protecting their information seriously.”
In the next section, we’ll explore best practices for implementing robust data protection for financial services, including encryption protocols that can help you meet these complex requirements while maintaining efficient operations.
Best Practices for Data Protection in Financial Services
When it comes to protecting sensitive financial information, there’s no room for half-measures. At Titan Technologies, we’ve seen how the right security practices can make all the difference for financial institutions in Central New Jersey and beyond.
Let’s talk about what really works when implementing data protection for financial services – not just theory, but practical approaches that keep your clients’ data safe without bringing operations to a standstill.
Implementing Strong Encryption Protocols
Think of encryption as your financial data’s invisible shield. It transforms readable information into scrambled code that’s meaningless without the proper key. For banks and financial firms, encryption isn’t just nice to have – it’s essential.
The financial industry standard typically involves Advanced Encryption Standard (AES) with 256-bit keys – essentially the Fort Knox of encryption methods. For secure data transmission and digital signatures, RSA encryption provides that extra layer of protection your clients expect.
Encryption needs to protect your data at every stage:
When it’s sitting in your databases (data at rest), when it’s moving across networks (data in transit), and even when it’s being actively used (data in use).
One of our clients in Edison was concerned about meeting PCI DSS requirements for their payment processing system. We implemented a comprehensive encryption solution that not only satisfied compliance but actually improved their system performance – proving that security doesn’t have to come at the cost of efficiency.
Key management is where many financial institutions stumble. Your encryption is only as strong as your key management practices. We recommend regular key rotation, secure storage methods, and strict access limitations. Think of encryption keys like the master keys to your building – you wouldn’t hand those out casually, would you?
According to Statista, the financial sector experiences more ransomware attacks than almost any other industry. Strong encryption is your first line of defense against these increasingly sophisticated threats.
Utilizing Multi-Factor Authentication (MFA)
Passwords alone just don’t cut it anymore. Multi-factor authentication adds crucial layers of security by requiring multiple forms of verification before granting access.
The beauty of MFA is its simplicity: combine something you know (like a password), something you have (like your phone), and sometimes something you are (like your fingerprint). This combination makes unauthorized access exponentially more difficult.
I still remember working with a community bank in Princeton that was hesitant about implementing MFA, worried their older customers would find it confusing. We developed a user-friendly approach with clear instructions, and within months, fraud attempts dropped dramatically while customer complaints were minimal.
MFA should be your standard for all access points – employee systems, customer portals, administrative tools, and third-party connections. The most effective implementations use adaptive authentication, which adjusts security requirements based on risk factors like location, device, and behavior patterns.
Data Backup and Recovery
In the financial world, data loss isn’t just inconvenient – it can be catastrophic. A solid backup strategy is your insurance policy against disasters both natural and digital.
We recommend following the time-tested 3-2-1 approach: maintain three copies of important data, store them on at least two different types of media, and keep one copy offsite or in the cloud. This isn’t just theory – it’s a practical approach that has saved several of our clients from potential disaster.
A regional credit union in New Brunswick learned this lesson the hard way when a power surge damaged their primary systems. Fortunately, their comprehensive backup solution (which we had implemented six months earlier) allowed them to restore operations with minimal disruption and no data loss.
Beyond just creating backups, you need to regularly test them. I’ve seen too many financial institutions find their backups were incomplete or corrupted only when they desperately needed to restore data. Regular testing, automated verification, and clear recovery procedures are essential components of a backup strategy that actually works.
For data protection for financial services, the right approach combines proven technologies with thoughtful implementation. The comparison table below highlights different encryption methods commonly used in financial services:
| Encryption Method | Strength | Best Used For | Implementation Complexity |
|---|---|---|---|
| AES-256 | Very High | Data at rest, sensitive files | Moderate |
| RSA-2048 | High | Digital signatures, key exchange | Complex |
| TLS 1.3 | High | Data in transit, web traffic | Low to Moderate |
| Blowfish | Moderate | Legacy systems | Low |
By implementing these proven practices, financial institutions can significantly reduce their vulnerability while maintaining the performance and accessibility their operations require. The goal isn’t just compliance – it’s creating a security foundation that enables growth and inspires confidence.
Overcoming Challenges in Data Protection for Financial Services
Let’s face it—protecting financial data isn’t always smooth sailing. Even with the best intentions, financial institutions often run into roadblocks that can make data protection for financial services feel like trying to solve a Rubik’s cube blindfolded. But don’t worry—these challenges have solutions, and we’re here to help you steer them.
Integrating New Software with Legacy Systems
If you’ve worked in financial services for any length of time, you’re probably familiar with this scenario: Your institution wants to implement cutting-edge security software, but your core banking platform was developed when floppy disks were still cool. It’s a common dilemma.
Many banks and credit unions find themselves running on systems that have served them faithfully for decades. These legacy systems handle millions of transactions flawlessly, but they weren’t designed with today’s security threats in mind.
When you try to connect modern security tools to these older systems, you might encounter compatibility headaches that make your IT team reach for the aspirin. Legacy systems often speak a different technical “language” than newer applications, creating potential security gaps where data could be exposed.
At a regional bank in Trenton we worked with, their 20-year-old core banking system couldn’t directly support modern encryption standards. Rather than ripping out their entire infrastructure (and breaking the budget), we created a secure middleware layer that acted as a translator between old and new systems. This approach maintained strong data protection for financial services without disrupting their operations.
The key to successful integration lies in careful planning. Before connecting any new system to your legacy infrastructure, conduct a thorough risk assessment. Identify potential vulnerabilities and develop specific strategies to address them. Sometimes, the solution might involve secure API gateways or data tokenization to protect information as it moves between systems.
Remember—you don’t have to modernize everything overnight. A phased approach often works better, allowing you to strengthen security incrementally while spreading costs over time.
Balancing Security and Usability
We’ve all been there: creating that perfect password with uppercase letters, lowercase letters, numbers, symbols, hieroglyphics, and possibly your childhood pet’s middle name—only to forget it five minutes later. When security becomes too cumbersome, people find workarounds, often creating bigger security risks.
The challenge for financial institutions is finding that sweet spot where data protection for financial services remains robust without driving customers (or employees) crazy. Too little security puts data at risk; too much frustrates users and pushes them toward dangerous shortcuts like writing passwords on sticky notes.
A credit union in Woodbridge came to us with an interesting problem: their super-secure login process was so complicated that they were drowning in password reset calls. Their intentions were good—they wanted maximum security—but the implementation was causing friction. We helped them redesign their authentication process to use contextual security, which adjusts the level of verification based on the risk level of the transaction and user behavior patterns.
The results spoke for themselves: a 35% drop in support calls related to login issues, happier customers, and—most importantly—stronger overall security. Sometimes less really is more.
Here’s what works when balancing security and usability:
Design with empathy by putting yourself in users’ shoes. Security measures should feel intuitive rather than intrusive. Provide clear explanations of why certain security steps are necessary—people are more accepting of friction when they understand its purpose. And always gather feedback from actual users to identify pain points in your security processes.
Perfect security doesn’t exist—but security that works consistently because people actually use it properly is far better than theoretically perfect security that gets bypassed.
At Titan Technologies, we’ve helped numerous financial institutions throughout Central New Jersey overcome these challenges. Whether you’re in Princeton struggling with legacy system integration or in Elizabeth trying to improve customer satisfaction with your security measures, we understand the unique demands of data protection for financial services and can help you steer these common problems.
Developing a Robust Data Protection Strategy
Building a strong defense for your financial institution doesn’t happen overnight. It requires thoughtful planning, consistent execution, and a willingness to adapt as threats evolve. Let’s explore how to create a protection strategy that truly works.
Risk Assessments and Cybersecurity Frameworks
Think of risk assessment as your financial institution’s regular health checkup. Just as you’d visit a doctor to catch potential health issues early, regular security assessments help identify vulnerabilities before they become major problems.
Starting with the basics, you’ll want to document all systems containing sensitive financial data. This inventory becomes your roadmap, showing you exactly what needs protection. Next comes the detective work – scanning for weaknesses in your systems and processes that could be exploited.
Threat analysis is equally important. What attack vectors are most likely to target your institution? Is it phishing attempts aimed at your employees? Vulnerabilities in your customer-facing applications? Or perhaps outdated systems with known security flaws?
Once you understand the threats, calculate their potential impact. Not all risks are created equal – some might cause minor inconvenience while others could threaten your institution’s very existence. This analysis helps you prioritize, addressing the highest-risk issues first rather than spreading resources too thin.
Many of our clients in Freehold and Red Bank have found tremendous value in adopting established cybersecurity frameworks. The NIST Cybersecurity Framework offers a comprehensive approach to managing security risk, while the CIS Controls provide a prioritized set of actions to protect critical systems. For those seeking international certification, ISO 27001 provides a globally recognized standard.
The impact of these frameworks is impressive. According to research from the SANS Institute and CIS, implementing just the first five CIS controls can prevent 85% of cyber attacks. Implement all 20, and that protection jumps to 97%. That’s the difference between leaving your door open uped versus installing a state-of-the-art security system.
Employee Training in Data Protection for Financial Services
Your team members are both your greatest asset and potentially your biggest vulnerability when it comes to data protection for financial services. Even the most sophisticated security technology can be undermined by a single employee clicking on a phishing link or using a weak password.
Effective training begins with security awareness basics. Everyone in your organization should know how to recognize phishing attempts, create and manage strong passwords, and understand physical security practices like clean desk policies and visitor protocols.
Beyond the basics, consider role-specific training. Your lending team needs different security knowledge than your IT staff or customer service representatives. Tailor education to job functions and access levels for maximum impact.
Regulatory compliance training is non-negotiable in the financial sector. Your team needs to understand relevant laws and regulations – not just what they require but why they matter. This understanding builds a culture of compliance rather than mere rule-following.
Clear incident reporting procedures are essential. When employees spot something suspicious, they should know exactly what to do and who to contact. As one cybersecurity expert puts it, “Educate and train employees on security protocols and identifying phishing or suspicious activities.” This vigilance forms your first line of defense.
Make training engaging and memorable. Simulated phishing campaigns show employees what real attacks look like. Gamified learning experiences turn security education into something employees actually enjoy. Micro-learning modules delivered regularly keep security top of mind without overwhelming staff. And department-specific case studies make abstract threats feel concrete and relevant.
Effective training isn’t a one-time event but an ongoing process. As threats evolve, so should your training program.
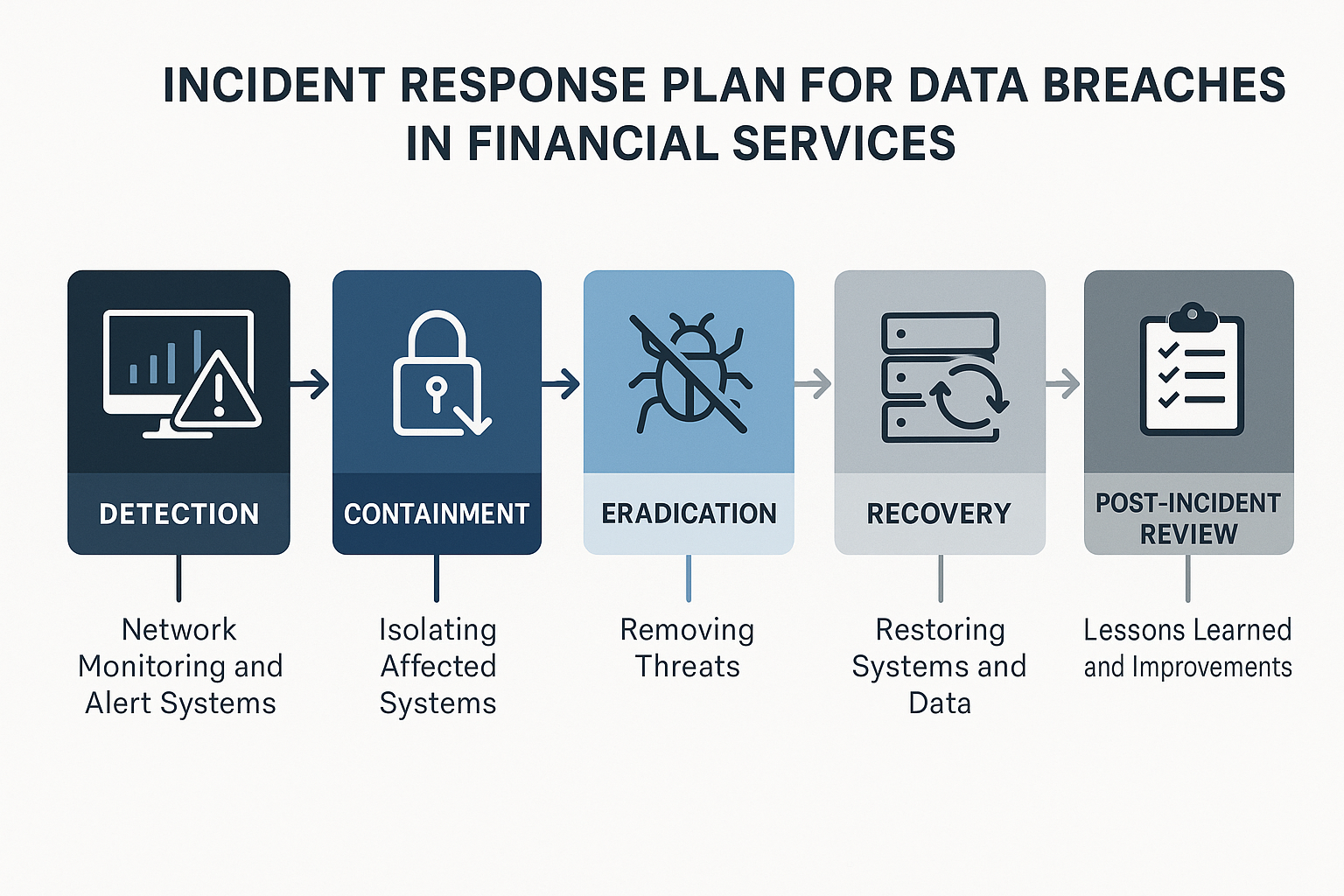
Incident Response and Data Breach Preparedness
Despite your best prevention efforts, security incidents may still occur. Having a well-rehearsed incident response plan is like having insurance – you hope you’ll never need it, but you’ll be incredibly grateful it’s there if you do.
A solid response plan starts with detection and analysis – identifying potential security incidents quickly and assessing their severity and scope. The sooner you spot a problem, the better your chances of containing it before significant damage occurs.
Containment strategies are your emergency brakes. These are the steps you’ll take to limit the spread and impact of a breach, such as isolating affected systems or temporarily disabling certain services. Think of it as creating firebreaks to stop a wildfire from spreading.
Once contained, you’ll move to eradication – removing the cause of the incident, whether that’s malware, compromised credentials, or an exploited vulnerability. This phase requires thoroughness and attention to detail to ensure the threat is completely eliminated.
Recovery brings systems back to normal operation, often in a phased approach starting with the most critical functions. This isn’t just about restoring data from backups – it’s about ensuring systems are secure before they’re brought back online.
The post-incident review might be the most valuable part of the process. What happened? How did it happen? What worked well in your response? What didn’t? These insights help prevent similar incidents and improve your response to future threats.
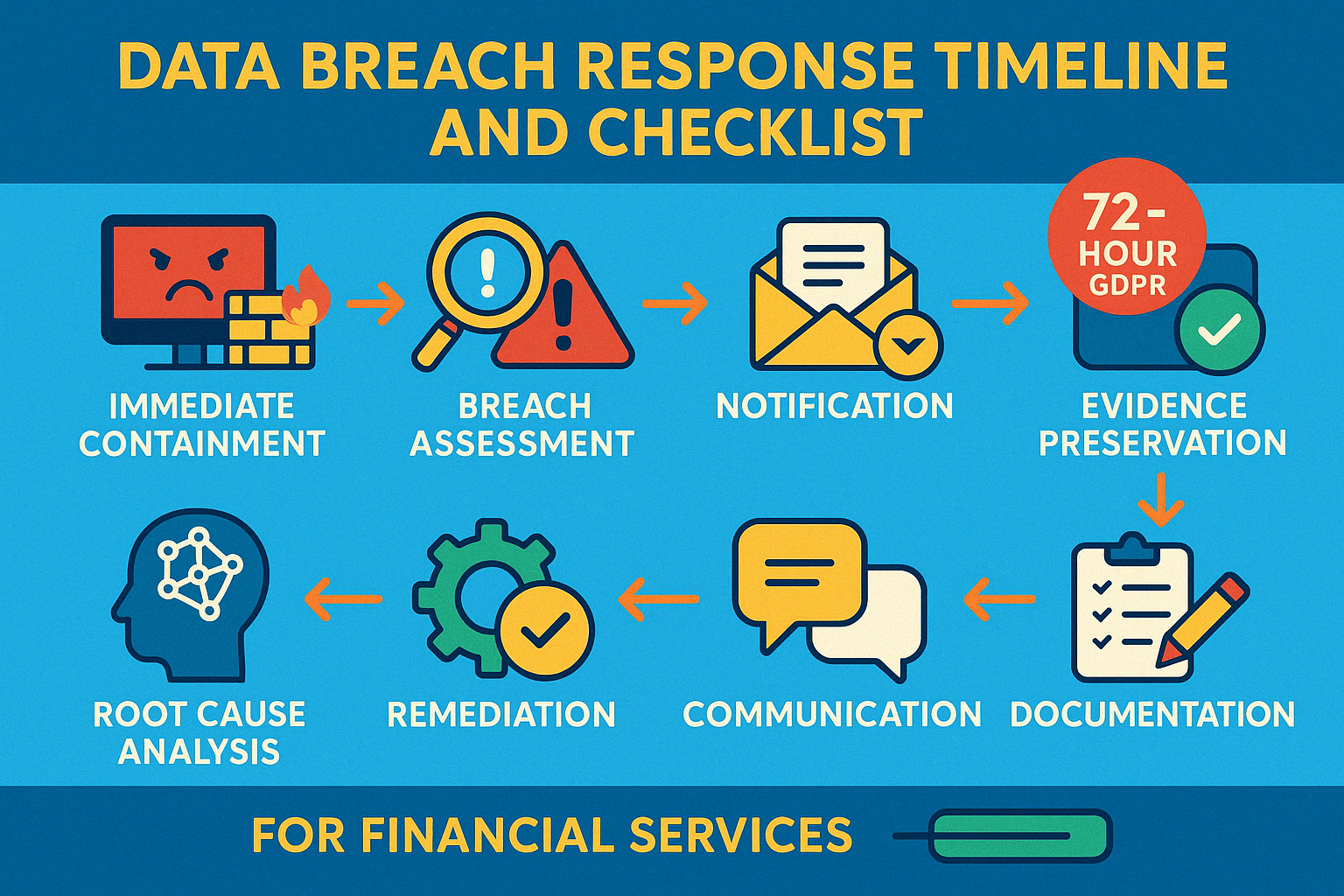
For financial institutions, breach notification requirements add another layer of complexity. Under regulations like GDPR, you have just 72 hours to report certain breaches. Your plan should clearly outline when to notify authorities, when to inform affected customers, what information to include, and who’s responsible for making these notifications.
Regular practice is essential. Tabletop exercises and simulations help ensure your response team can execute the plan under pressure. These drills should cover various scenarios – from data breaches to ransomware attacks – so your team is prepared for whatever comes their way.
At Titan Technologies, we’ve helped numerous financial institutions throughout Central New Jersey develop and test incident response plans that align with both regulatory requirements and business needs. The peace of mind that comes from knowing you’re prepared for the worst is invaluable.
Compliance and Regulatory Considerations
Let’s face it – nobody gets excited about compliance paperwork. But in the financial world, staying on top of regulations isn’t just about avoiding fines – it’s about protecting your customers and your reputation. When it comes to data protection for financial services, compliance isn’t optional – it’s essential.
Managing Compliance in Data Protection for Financial Services
Think of compliance management as your financial institution’s immune system. When it’s working well, you hardly notice it. When it fails… well, that’s when the headaches begin.
Creating a culture of compliance starts at the top. Your leadership team needs to champion compliance efforts and make it clear that cutting corners isn’t an option. This means establishing clear roles for who’s responsible for what aspects of compliance – from the board room to the front line.
Good policies are the backbone of compliance, but they’re only effective if they’re living documents. I’ve seen too many financial institutions with beautifully written policies gathering digital dust on a shared drive. Your policies should be regularly reviewed, updated, and – most importantly – actually followed by your team.
Documentation might seem tedious, but it’s your best friend during an audit. As the old compliance saying goes, “if it isn’t documented, it didn’t happen.” Keep detailed records of your compliance activities, decisions, and the reasoning behind them. This creates an audit trail that demonstrates your commitment to following regulations.
One approach that works well for our clients in Newark and Elizabeth is implementing a compliance calendar. This simple tool tracks important regulatory deadlines, scheduled assessments, policy reviews, and training requirements. It helps transform compliance from a reactive scramble into a proactive, manageable process.
Regular compliance audits aren’t just about finding problems – they’re learning opportunities. These reviews should be conducted by people who understand both the technical aspects of data security and the regulatory requirements you face. When issues are found (and they will be), address them promptly and transparently.
“Compliance isn’t about checking boxes,” one of our banking clients in Trenton recently told me. “It’s about building trust with our customers that we’re handling their data with care and integrity.” That perspective transforms compliance from a burden into a competitive advantage.
Leveraging Technology for Compliance
Technology can be your greatest ally in managing the complex web of regulations affecting data protection for financial services. The right tools don’t just make compliance easier – they make it more effective.
Compliance management systems serve as your central command center, tracking requirements and activities across your organization. These platforms can alert you to upcoming deadlines, assign tasks to team members, and provide real-time visibility into your compliance status.
One of the biggest compliance challenges is simply knowing where your sensitive data lives. Data findy and classification tools automatically scan your systems to identify and categorize sensitive information. This is especially valuable for financial institutions with complex IT environments spanning legacy systems and modern cloud applications.
Policy management software streamlines the creation, distribution, and acknowledgment of policies. Instead of wondering if employees have read the latest security procedures, these tools track who has reviewed what policies and when. This creates accountability and ensures everyone is working from the same playbook.
Regulatory change management tools help you stay ahead of the constantly evolving compliance landscape. These solutions monitor for regulatory updates and help you assess how changes impact your business. For smaller financial institutions in Central New Jersey that don’t have large compliance departments, these tools can be particularly valuable.
At Titan Technologies, we’ve helped credit unions and community banks in places like Red Bank and Freehold implement technology solutions that transform compliance from a burden into a business advantage. The right technology doesn’t replace human judgment – it improves it by automating routine tasks and highlighting areas that need attention.
Compliance technology is most effective when it’s integrated into your overall data protection for financial services strategy. Isolated compliance tools create silos that can actually increase risk. Look for solutions that complement your existing security technologies and business processes.
As regulations continue to evolve, the financial institutions that thrive will be those that view compliance not as a cost center but as an opportunity to strengthen their data protection practices and build customer trust. With the right approach and tools, compliance can become a competitive advantage rather than just another regulatory hurdle.
Frequently Asked Questions about Data Protection for Financial Services
What are the key regulations governing data protection in financial services?
Navigating the regulatory landscape for financial data protection can feel like trying to solve a puzzle with constantly changing pieces. Let’s break down the major regulations you need to know about:
Gramm-Leach-Bliley Act (GLBA) forms the cornerstone of financial privacy in the U.S. It’s all about transparency and protection – financial institutions must clearly explain how they share customer information and implement robust safeguards to protect sensitive data. Think of it as the “no surprises” rule for how your financial information is handled.
The General Data Protection Regulation (GDPR) casts a wide net for any organization handling EU citizens’ data. It’s comprehensive and strict, giving individuals significant control over their personal information. If you’re working with European customers, this regulation demands your attention with its requirements for explicit consent and prompt breach notifications.
When credit card information enters the picture, the Payment Card Industry Data Security Standard (PCI DSS) takes center stage. It’s essentially a security playbook that organizations must follow to protect cardholder data.
For financial institutions with California customers, the California Consumer Privacy Act (CCPA) adds another layer of compliance by giving residents specific rights regarding their personal information. Similarly, the New York Department of Financial Services Cybersecurity Regulation requires financial institutions to implement thorough cybersecurity programs.
Don’t forget about the Bank Secrecy Act (BSA) and Anti-Money Laundering (AML) requirements. While they’re primarily focused on preventing financial crimes, they have significant implications for how you handle and protect data.
What makes this challenging is that the regulatory landscape never stands still. New laws and amendments appear regularly, requiring financial institutions to stay informed and adaptable. It’s like hitting a moving target – challenging but necessary for maintaining compliance and customer trust.
How can financial institutions secure data while maintaining user-friendly applications?
The tug-of-war between security and usability doesn’t have to end in compromise. With thoughtful design, you can achieve both robust data protection for financial services and a smooth user experience.
Risk-based authentication offers a smart approach – applying different levels of security based on what the user is trying to do. Checking an account balance might require basic security, while transferring large sums triggers additional verification steps. This way, security feels proportional rather than burdensome.
Many of our clients in Central New Jersey have found success with progressive security measures. This approach keeps everyday functions simple while reserving stronger security for higher-risk actions. It’s like having different locks for different doors in your house – the valuable items get extra protection.
Behind-the-scenes security measures like device fingerprinting and behavioral analytics provide seamless authentication without interrupting the user’s journey. These technologies work quietly in the background, identifying suspicious activities without constantly asking users to verify their identity.
When security measures are necessary, clear communication makes all the difference. Explaining in simple terms why certain security steps exist helps users understand their purpose rather than just seeing them as obstacles. Similarly, maintaining a consistent user experience across security features helps users steer them confidently.
Biometric authentication methods have been game-changers for many financial institutions. Fingerprint or facial recognition provides strong security with minimal effort from users – just a quick scan and they’re in. When implemented thoughtfully, these methods significantly improve both protection and user satisfaction.
The final piece of the puzzle is regular user testing. By observing how real people interact with security features, you can identify and eliminate friction points before they become problems. At Titan Technologies, we’ve helped numerous financial institutions in places like Princeton and Newark redesign their security interfaces based on user feedback, resulting in both stronger protection and happier customers.
What steps should be taken in the event of a data breach?
Even with the best protections in place, breaches can still happen. When they do, having a clear response plan makes all the difference between a manageable incident and a full-blown crisis.
The moment a breach is detected, immediate containment becomes the priority. This might mean taking affected systems offline to prevent further data loss – like closing a gate to stop water from flooding through. Speed matters here, as every minute could mean more compromised data.
Next comes a thorough breach assessment to determine what information was affected and how the breach occurred. This detective work forms the foundation for all subsequent actions and communications.
Regulations like GDPR require organizations to report breaches to authorities within 72 hours of findy. Different notification requirements apply depending on your location and the types of data involved, so it’s crucial to understand your specific obligations beforehand.
Throughout the response, evidence preservation is essential. Secure logs and other digital evidence that might help investigate the breach – think of it as preserving a crime scene for investigators.
Once the immediate crisis is contained, conduct a root cause analysis to identify how the breach happened and what vulnerabilities were exploited. This isn’t about placing blame but about understanding weaknesses that need addressing.
Remediation follows naturally from this analysis – fixing the vulnerabilities that allowed the breach to occur in the first place. This might involve patching systems, changing procedures, or implementing new security controls.
Clear, honest communication with customers and stakeholders builds trust even in difficult circumstances. People appreciate transparency about what happened and what you’re doing to protect their information going forward.
Throughout the process, maintain detailed documentation of the breach and your response actions. This serves both compliance purposes and provides valuable information for improving your security posture.
Finally, conduct a post-breach review to analyze how well your response worked and identify improvements for the future. Even the best-handled breaches offer lessons for strengthening your defenses.
At Titan Technologies, we’ve helped financial institutions in Edison, Elizabeth, and throughout Central New Jersey develop and test breach response plans that meet regulatory requirements while protecting both data and reputation. The goal isn’t just to recover from a breach but to emerge stronger and more resilient than before.
Conclusion
When it comes to data protection for financial services, we’re not just talking about checking boxes for regulators—we’re talking about the lifeblood of your financial institution. In today’s world where digital threats lurk around every corner, protecting your customers’ sensitive information isn’t optional—your very survival.
Throughout this guide, we’ve explored the many facets of financial data protection. From technical safeguards to employee training, from incident response to regulatory compliance, we’ve covered the crucial elements that make up a comprehensive protection strategy.
Think of your data protection approach as a shield with multiple layers. The outer layer consists of robust technical defenses like strong encryption and multi-factor authentication that keep the bad actors at bay. The middle layers include your policies, procedures, and employee training programs that ensure everyone knows their role in keeping data safe. And at the core, you have your incident response plans—your safety net for when (not if) something goes wrong.
I’ve seen how devastating data breaches can be for financial institutions. Beyond the immediate financial impact, the loss of customer trust can haunt an organization for years. That’s why at Titan Technologies, we’re passionate about helping financial businesses throughout Central New Jersey build protection strategies that actually work in the real world.
Our team understands that every financial institution is unique. The neighborhood credit union in Woodbridge faces different challenges than the investment firm in Princeton or the community bank in Trenton. That’s why we don’t believe in one-size-fits-all solutions. Instead, we work closely with you to understand your specific needs, risks, and goals.
Data protection for financial services isn’t a destination—it’s a journey. Threats evolve, regulations change, and your protection strategies need to keep pace. Think of it as regular maintenance for your car—you wouldn’t go years without changing the oil, and you shouldn’t let your data protection strategies gather dust either.
From our locations across Central New Jersey—Edison, Elizabeth, Lakewood, Newark, Trenton, Princeton, New Brunswick, Matawan, Woodbridge, Freehold, and Red Bank—our team of cybersecurity experts is ready to help you steer this complex landscape. We’re here to ensure that your sensitive financial data remains secure, your regulatory compliance stays on track, and most importantly, your customers’ trust remains unshaken.
The financial world is changing rapidly, but one thing remains constant: the need to protect your most valuable asset—your data. By implementing the strategies we’ve discussed and partnering with experienced professionals, you can face the future with confidence, knowing that your financial data is secure against whatever threats may come.
Ready to strengthen your financial institution’s data protection? We’d love to chat about how Titan Technologies can help you develop a protection strategy that meets your unique needs. After all, in financial data protection, you don’t have to go it alone.
Related content about data protection for financial services:
– Data Protection and Management
– Data Privacy Solutions