Data security solutions are the backbone of any robust IT strategy aimed at protecting sensitive data. In today’s digital landscape, these solutions are essential for organizations seeking to guard against data breaches, ensure compliance with regulations, and maintain the integrity of their data.
Protect Sensitive Data: From client information to proprietary business insights, safeguarding sensitive data ensures that critical information remains confidential and secure.
Ensure Compliance: Staying compliant with regulations like HIPAA, GDPR, and PCI-DSS is not just a legal requirement but a strategic necessity to protect your company’s reputation and finances.
Prevent Unauthorized Access: Using methods like encryption, access controls, and data classification, businesses can effectively shield data from unauthorized access.
In an era where digital threats are continually evolving, understanding these solutions is the first step towards fortifying your business against potential risks. Whether you’re a small business owner in Central New Jersey or a large multinational, integrating comprehensive data security measures is crucial for sustaining your business operations securely and efficiently.
Simple guide to data security solutions terms:
- data privacy solutions
- data protection governance risk management and compliance
- data protection security controls
Understanding Data Security Solutions
Data security solutions are your shield against digital threats. They protect sensitive information, ensure compliance, and keep your business running smoothly. Let’s break down what these solutions involve.
Data Protection Throughout Its Lifecycle
Data isn’t static. It moves and changes, and so do the threats against it. That’s why data protection is essential at every stage of its lifecycle—whether data is at rest, in use, or in transit.
Data at Rest: This is information stored on devices or networks. Protect it with encryption and access controls.
Data in Use: When data is being accessed and processed, it’s vulnerable. Use strong authentication methods to ensure only authorized users can access it.
Data in Transit: Information being sent across networks can be intercepted. Secure it with encryption to keep it safe from prying eyes.
Navigating Compliance Regulations
Compliance isn’t just about avoiding fines; it’s about building trust and protecting your reputation. Regulations like HIPAA, GDPR, and PCI DSS set the standards for how data should be handled. Non-compliance can lead to hefty fines and a loss of customer trust.
HIPAA: Protects health information. Essential for healthcare providers.
GDPR: Focuses on personal data protection for EU citizens. Important for any business operating in or with the EU.
PCI DSS: Ensures secure handling of credit card information. Critical for businesses that process card payments.
Each regulation has specific requirements, but they all emphasize the importance of protecting sensitive data. Implementing the right data security solutions helps ensure you meet these requirements and protect your business from legal and financial risks.
Why It Matters
Understanding and implementing these solutions is not just a technical necessity—it’s a strategic advantage. By protecting data and ensuring compliance, you safeguard your business’s future. This is especially crucial in today’s digital world, where threats are constant and evolving.
In the next section, we’ll explore the top data security solutions you can implement to protect your organization effectively.
Top Data Security Solutions
In today’s digital landscape, safeguarding your data is more critical than ever. Here, we’ll dive into the top data security solutions that can help shield your business from threats and ensure compliance with regulations.
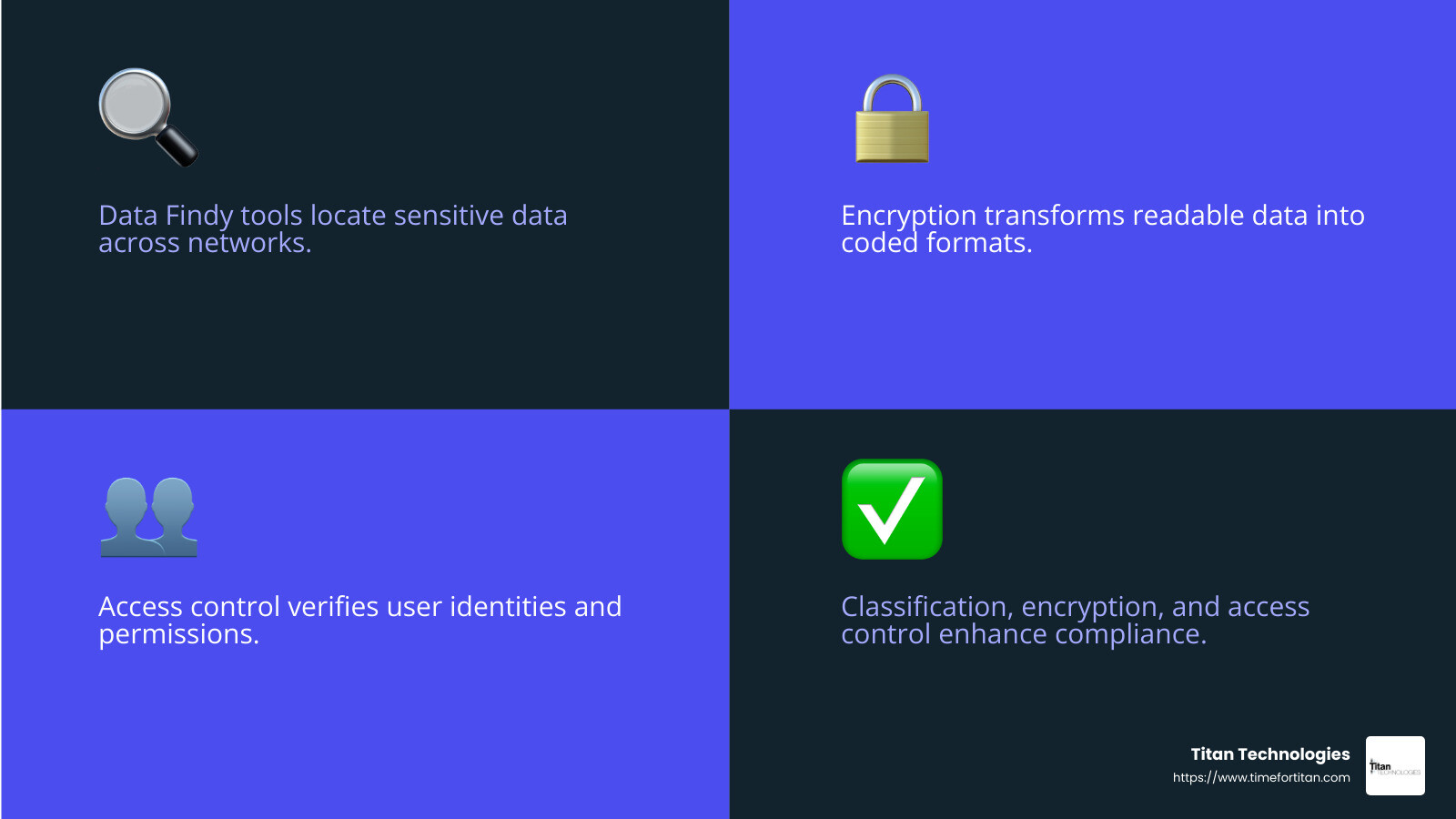
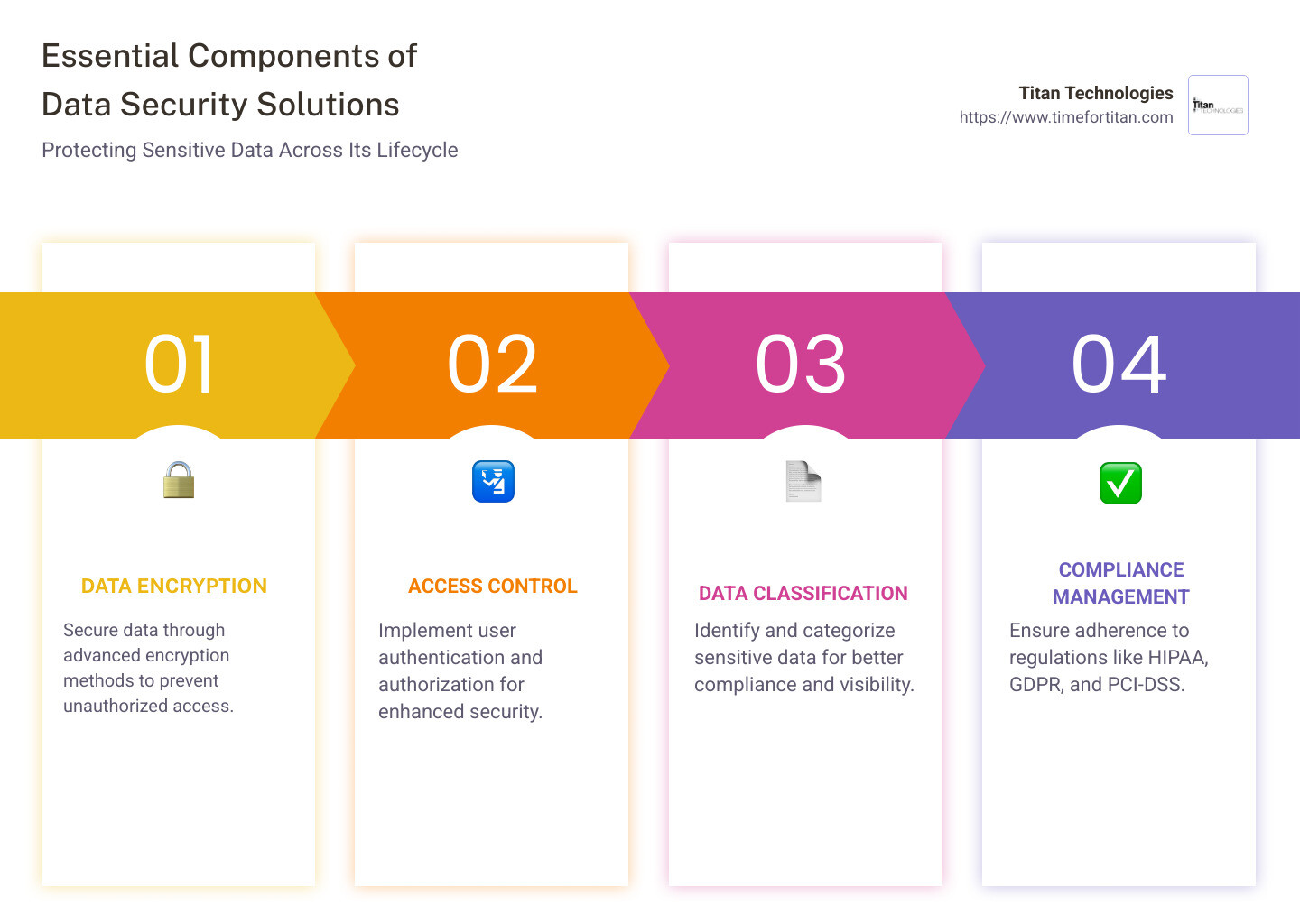
Data Findy and Classification
Understanding what data you have and where it resides is the first step to securing it. Data findy and classification tools help you locate sensitive data across your network, whether on-premises or in the cloud. These tools scan your repositories and classify data based on its sensitivity and compliance requirements.
Why It Matters: Knowing where your sensitive data is stored allows you to apply appropriate security measures. This step is crucial for compliance and helps prevent accidental data exposure.
Compliance and Visibility: By classifying data, you can ensure it meets regulations like GDPR or HIPAA. This also improves visibility, making it easier to manage and protect your data.
Data Encryption
Encryption is a cornerstone of data protection. It transforms readable data into a coded format, ensuring that only authorized users can access it. There are various encryption methods available, each suited for different types of data and use cases.
Data at Rest Encryption: Protects data stored on devices by encrypting it. Even if a device is lost or stolen, the data remains secure.
Data in Transit Encryption: Secures data as it moves across networks, preventing interception by unauthorized parties.
Secure Data: Encryption ensures that sensitive information remains confidential and intact, reducing the risk of data breaches and financial losses.
Access Control
Controlling who can access your data is vital. Access control involves verifying user identities and granting permissions based on their role and necessity.
User Authentication: Ensures that only verified users can access sensitive data. This can involve passwords, biometric scans, or security tokens.
Authorization: Determines what actions a user can perform once authenticated. This ensures users only access data relevant to their role.
Multi-Factor Authentication (MFA): Adds an extra layer of security by requiring users to provide two or more verification factors. This significantly reduces the risk of unauthorized access.
Implementing these data security solutions not only protects your sensitive information but also ensures compliance with various regulations. By securing your data through classification, encryption, and access control, you can build a robust defense against digital threats and safeguard your business’s future.
In the next section, we’ll explore how to effectively implement these solutions to manage risks and improve your organization’s security posture.
Implementing Data Security Solutions
Implementing data security solutions requires a strategic approach that focuses on risk management, security policies, and organizational controls. Here’s how you can effectively secure your data:
Risk Management
Risk management is all about identifying and mitigating potential threats to your data. Start by conducting a thorough risk assessment. This helps you understand where your vulnerabilities lie and what risks your organization faces.
Identify Risks: Look for potential threats both inside and outside your organization. This includes cyber threats, human errors, and physical risks.
Prioritize Risks: Not all risks are created equal. Focus on those that could have the most significant impact on your business.
Mitigate Risks: Implement controls to reduce the likelihood and impact of these risks. This could include technical solutions like firewalls and intrusion detection systems, as well as administrative controls like training employees on data security best practices.
Security Policies
Having strong security policies is crucial for protecting your data. These policies define how your organization handles data and what measures are in place to keep it secure.
Create Clear Policies: Develop policies that outline how data is to be accessed, handled, and protected. Ensure they comply with relevant regulations like GDPR or CCPA.
Educate Employees: Make sure everyone in your organization understands these policies. Regular training sessions can help employees recognize potential threats and know how to respond.
Regular Reviews: Policies should not be static. Regularly review and update them to reflect new threats and changes in your organization.
Organizational Controls
Organizational controls are the processes and procedures that ensure your data security measures are effective.
Access Control: Limit access to sensitive data to only those who need it to perform their job. Use role-based access controls and regularly review permissions.
Monitoring and Auditing: Continuously monitor access and activity to detect any unusual behavior. Regular audits can help ensure compliance and identify areas for improvement.
Incident Response: Have a plan in place for responding to data breaches or security incidents. This should include steps for containment, investigation, and communication.
By focusing on risk management, security policies, and organizational controls, you can create a robust data security framework. This not only protects your data but also builds trust with customers and ensures compliance with regulations.
In the next section, we’ll address some frequently asked questions about data security solutions, providing clarity on what they are and why they’re crucial for your business.
Frequently Asked Questions about Data Security Solutions
What is a data security solution?
A data security solution is a collection of technologies and practices designed to protect your data from theft, loss, or unauthorized access. These solutions help ensure that your sensitive information remains secure throughout its lifecycle. They include methods like encryption, access control, and real-time monitoring. By implementing these measures, businesses can prevent data breaches and maintain the integrity of their data.
Why is data security important?
Data security is crucial for several reasons:
Compliance: Many industries have strict regulations, such as GDPR and HIPAA, that require businesses to protect sensitive data. Failing to comply can result in hefty fines and legal consequences.
Sensitive Data Protection: Protecting customer and company data is essential to prevent it from falling into the wrong hands. This includes personal information, financial data, and proprietary business information.
Financial Risks: Data breaches can lead to significant financial losses, not just from direct theft but also from the costs associated with fixing breaches, legal fees, and damage to reputation.
Trust: Maintaining strong data security measures builds trust with customers, who expect their information to be handled safely and responsibly.
How can small businesses afford data security solutions?
Small and medium-sized enterprises (SMEs) can often feel overwhelmed by the cost of data security solutions. However, there are affordable and cost-effective options available:
Flexible Solutions: Many vendors offer scalable solutions designed specifically for SMEs, allowing businesses to pay only for what they need.
Managed Services: Partnering with a managed IT services provider can help SMEs implement robust security measures without the need for a large in-house IT team.
Prioritize Needs: Focus on the most critical security measures first, such as encryption and access control, to maximize protection while staying within budget.
Investing in data security solutions is not just a cost but a crucial step in safeguarding your business’s future. By choosing the right solutions, SMEs can protect their data without breaking the bank.
In the next section, we’ll conclude our guide by highlighting how Titan Technologies can help you with managed IT services and cybersecurity solutions.
Conclusion
As we wrap up our guide on data security solutions, it’s clear that protecting your data is not just a technical requirement but a strategic necessity for businesses today. With the increasing complexity of cyber threats, having a robust data security strategy is essential.
At Titan Technologies, we understand the challenges businesses face in maintaining secure and efficient operations. Our managed IT services and cybersecurity solutions are designed to provide peace of mind, ensuring your data is protected against evolving threats.
Our professional team offers fast, reliable support with a 100% satisfaction guarantee. Whether you’re in Edison, Trenton, or any other part of Central New Jersey, we’re here to help you implement the right security measures custom to your needs.
By choosing Titan Technologies, you gain access to:
Expert Guidance: Our team stays up-to-date with the latest security trends and technologies, ensuring your business is always protected.
Comprehensive Solutions: From data encryption to multi-factor authentication, we offer a wide range of services to cover all aspects of data security.
Cost-Effective Options: We provide scalable solutions that fit your budget, making it possible for businesses of all sizes to afford top-notch security.
Protecting your business’s data is a critical investment in your future. Let us help you steer data security with confidence.
For more information on how we can support your business, visit our services page to explore our offerings and get in touch with our team. Together, we can fortify your data and ensure your business thrives in a secure environment.